Do you suspect that your partner has a secret life or hides things from you?
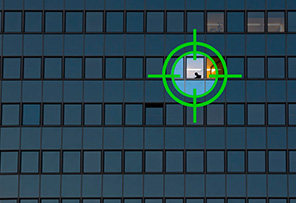
The private investigators at C.M.I can help you!. We offer you safe, professional and discreet research with excellent results. We are working according to the law to ensure that all our customers achieve the best possible results and thus always arrive with discretion to the truth. We understand that you may feel uncomfortable at your first contact with a Private Researcher, that’s why our team is friendly, professional and experienced to ensure that you receive excellent and confidential advice every time.
We understand the emotional problems associated with marriage, relationships, and other private affairs, and we handle all cases, from high affair cases to small discreet family issues with absolute confidentiality.